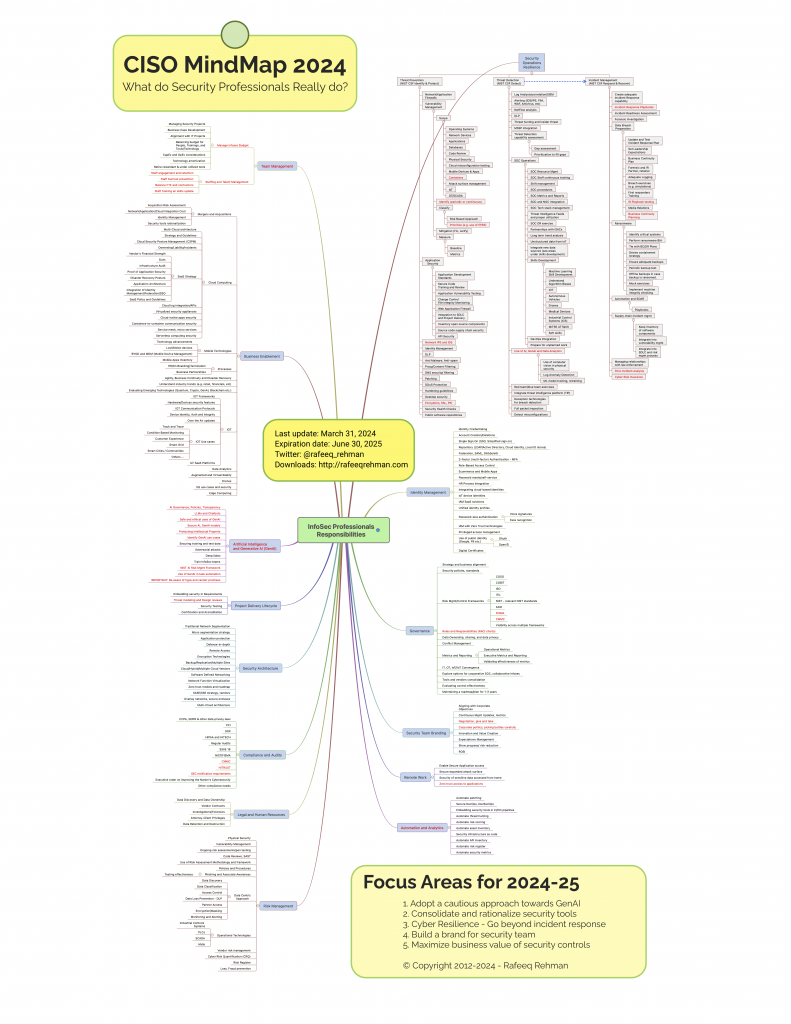
Many individuals outside the realm of cybersecurity often underestimate the intricacies involved in a security professional’s role. Since its inception in 2012, the CISO MindMap has served as a valuable educational resource, offering insights into CISO responsibilities and aiding security professionals in crafting and enhancing their security programs. Continuously adapting to reflect the evolving landscape of cybersecurity, the CISO MindMap has been updated to accommodate the latest developments in the field. Here is the most recent iteration of the CISO MindMap for 2024, featuring numerous enhancements and fresh recommendations for the year 2024-25.
Don’t forget to review recommendations for 2024-25 described below and to subscribe to my blog.
Click here to download high resolution PDF version of the CISO MindMap 2024
Summary of Changes to 2024 CISO MindMap
With time, the responsibilities of security professionals are only increasing. Why? Technology is changing fast, bringing new ways of doing business, continuous adoption of Cloud, and extremely fast evolving GenAI technology with many applications. Not only the Infosec professionals are “expected” to deeply understand these technologies, they are also tasked with providing policies/guidance on how to secure them. For this reason, every year you find new things on the CISO MindMap. At the same time, some items are changed or removed from the CISO MindMap depending upon their relevance. In the latest CISO MindMap, modified and new items are marked in red color for your convenience.
Other noticeable changes include:
- Artificial Intelligence and GenAI – MindMap now has a dedicated section on Artificial Intelligence and GenAI, reflecting insights from security leaders. GenAI’s rapid development is exciting, but measured caution is advised until the field matures further.
- Removing Redundancy and Overlaps – Removed some redundancies and overlaps in different sections. I also moved some elements of the MindMap to more relevant categories.
- Security Team Branding – An integral aspect of the CISO’s role involves effectively advocating for information security across diverse stakeholders. Drawing from valuable insights provided by experienced CISOs, we have expanded the section on ‘Security Branding’ in response to their feedback. This includes essential skills such as negotiation, executive engagement, strategic prioritization, and tactful decision-making. These are identified as key areas where new CISOs often encounter challenges, and thus, warrant special attention.
- Expiration Date – A common issue is that many professionals still have older CISO MindMap copies. Like last year, I added an “expiration date” to let people know when they should stop using a particular version. The expiration date for the 2024 CISO MindMap is the end of June 2025. The next version will be published before the current version expires.
CISO MindMap Updates Methodology
Every update to the CISO MindMap undergoes thorough consideration, research, and attention to detail. In addition to my ongoing engagements with industry leaders, various methods are employed to ensure we capture the pulse of the cybersecurity landscape:
- Conducting interviews with experts
- Distributing surveys to gather insights
- Leveraging LinkedIn for targeted questions and discussions
- Analyzing feedback and comments from previous versions of the CISO MindMap
- Staying abreast of industry news and conducting in-depth analysis
Furthermore, I’d like to express my gratitude to the contributors whose valuable insights have enriched this endeavor. The ‘Acknowledgments‘ section of this blog post includes their names and LinkedIn profiles as a token of appreciation.
Are you Accountable for Everything in the CISO MindMap?
Security is inherently a collaborative effort, and the role of the CISO entails providing consultative guidance in various areas outlined within the CISO MindMap. It’s crucial to discern between areas where direct ownership and accountability are necessary and those where consultation is the primary function. Within any organization, numerous stakeholders are involved, and a common pitfall is the lack of clearly defined boundaries for each role.
My recommendation is to establish a RACI (Responsible, Accountable, Consulted, Informed) matrix, which serves as a standardized methodology for delineating roles and responsibilities among stakeholders [6]. By mapping out tasks and corresponding roles within this framework, clarity is achieved, ensuring that each stakeholder understands their level of involvement and contribution to the overall security landscape.
Focus Areas and Recommendations for 2024-2025
Each year, I offer my recommendations as a practitioner, drawing insights from discussions with information security leaders. My approach strives for objectivity, steering clear of hype and focusing solely on data-driven research. Though unintended biases may exist, the goal remains to propose actionable steps viable within a short to mid-range timeframe. These recommendations do not constitute future predictions; rather, they address the immediate needs for enhancing security programs.
Selecting a concise set of recommendations is always a challenge for me. While the list provided below may be longer than I’d prefer, I aim to offer a comprehensive array of considerations for your reflection. Followers of the MindMap will notice both recurring suggestions from previous years and novel additions, providing a blend of continuity and fresh insights.
I’m genuinely interested in hearing your perspective on these recommendations and understanding whether they resonate with your experiences and insights. Your feedback, whether in agreement or disagreement, provides valuable insights that can help refine and improve our approach to addressing security challenges. So, please feel free to share your thoughts and insights on these recommendations—whether you support them or have reservations—so we can engage in a constructive dialogue to further enhance our security strategies.
Recommendation 1: Adopt a Cautious Approach Towards GenAI
GenAI has become a focal point of discussion, rapidly evolving within the technological landscape. The Wall Street Journal reported Amazon’s unprecedented investment in an AI startup, reflecting the significant momentum in this domain. In 2023, investments in Generative AI companies exceeded $29 billion [1]. Furthermore, numerous open-source solutions are emerging within the GenAI market [2]. Amidst the buzz, it’s important to maintain a discerning approach.
Security professionals approach GenAI from three primary perspectives:
- Utilization within security practices: Emphasizing enhanced productivity and the exploration of automation opportunities for routine tasks.
- Safeguarding GenAI in corporate environments: Establishing GenAI centers of excellence to ensure governance, policy adherence, and protection against potential attacks. Aligning business and cybersecurity strategies to accommodate GenAI.
- Monitoring malicious use of GenAI: While not yet a cause for alarm, it’s essential to remain vigilant regarding the evolving applications of GenAI for malicious purposes.
Although every security vendor touts AI integration within their products and services, it’s prudent to avoid succumbing to hype and refrain from significant investments in GenAI technology for security purposes at this stage. It’s anticipated that over the next 12-18 months, clear market leaders will emerge from the current phase of hype and use cases for Cybersecurity will be better defined. At this stage, it is better to educate oneself and explore use cases such as automation and productivity enhancement.
Recommendation 2: Consolidate and Rationalize Security Tools
No matter the size of your InfoSec budget, it is prudent to take a more critical look at security programs and find ways of ways for program management. An average organization is using a large number of technologies, by some estimates as high as 47, according to a Ponemon survey. Yet many security leaders don’t know if Cybersecurity tools are working. Accumulating more security tools doesn’t necessarily lower risk; rather, it amplifies the necessity for maintaining expertise within security teams. There is a need for consolidation and rationalization of security tools by deeply exploring Return on Investment (ROI) of these tools. When rationalizing the need for tools, consider factors such as functionality overlap, available expertise within the team to effectively utilize the tool, and the innovation on the side of vendors. You may be surprised to find shelfware. In some cases open source tools may work just fine as well.
Recommendation 3: Cyber Resilience – Go Beyond Incident Response
Building upon last year’s recommendation, it’s evident that in numerous organizations, security incident response remains separate from business continuity and disaster recovery functions. It’s imperative to assess ransomware defenses, detection, and response capabilities comprehensively. Conducting a business impact analysis is essential to identify critical processes, applications, and data.
Moreover, testing the ability to restore systems and data within an acceptable timeframe is crucial. Merely possessing backups is insufficient; the capability to rebuild impacted systems and restore backups promptly is vital for restoring normal business operations following security incidents.
Recommendation 4: Build a Brand for Security Team
The role of a CISO is inherently public-facing, demanding continuous engagement with technology and business leaders. While the message being conveyed holds significance, the credibility of the messenger is equally vital. To better serve the interests of the business, it’s imperative to equip security team members with skills beyond technical expertise, especially those who are aspiring to be leadership roles in future.
This includes training in business acumen, value creation, influencing without authority, and enhancing human experience. Emphasizing these aspects is not new; however, it’s crucial to maintain focus on the fact that information security teams operate within a broader context and must facilitate business objectives while collaborating effectively with others.
Skills such as negotiation, compromise, and strategic decision-making play pivotal roles in establishing both personal and team credibility, ultimately contributing to the enhancement of the overall brand.
Recommendation 5: Maximize Business Value of Security Controls
The proliferation of security and compliance controls often creates friction between security and other technology teams. However, not all controls carry equal weight, and some may offer minimal value in terms of risk reduction and business enhancement. It is advisable to conduct a thorough assessment of each control, evaluating its effectiveness and business impact.
CISOs should devise a strategy to phase out low-value controls within the next 12-18 months, thereby eliminating unnecessary maintenance costs. This proactive approach ensures resources are allocated efficiently, focusing efforts on controls that truly contribute to mitigating risks and driving business value
How to Use CISO MindMap?
Have you ever been asked to explain what you do as a security professional? The CISO MindMap offers a comprehensive solution for addressing this question and clarifying the intricacies of the role. Many professionals have attested to its efficacy in elucidating the complexities of the CISO position, particularly when communicating with a business audience.
Here are some ways in which the CISO MindMap proves to be immensely valuable:
- Facilitating conversations with fellow technology professionals.
- Instrumental in the design and refinement of security programs.
- Adopted by certain security vendors for raising awareness.
- Employed in CISO group discussions and community meetings.
- Aiding aspiring security professionals in understanding the industry landscape and charting their career paths.
- Serving as an educational and awareness-raising tool.
Obviously there is a lot on this MindMap. The stress on people who have these responsibilities is real. If nothing else, this MindMap should help leaders recognize that stress and do something about it. I covered this topic (stress) in my latest book Cybersecurity Arm Wrestling: Winning the perpetual fight against crime by building a modern Security Operations Center (SOC) as well.
What are They Saying?
Following are some comments on CISO MindMap LinkedIn post from 2023.
- Michael Restivo – “One of the most valuable documents around. Love this Rafeeq.”
- Chris Novak – “Always a great asset! Thanks for all that you do for the cybersecurity community!”
- Muath AlHomoud – “Great insight Rafeeq Rehman always inspiring”
- Christophe Foulon – “Insightful as always, Rafeeq Rehman”
- Matthew P. – “Thanks for updating this. I think this makes a really useful tool when talking to the next generation about careers in security being able to demonstrate the breadth of what we can get involved in is quite eye opening”
- David Elfering – “Thank you! I review security programs as part of my work; your outline is fantastic. As a CISO, I regularly reviewed it, and as a consultant/advisor, I can see even more clearly how others would benefit.”
- Alan Ng – “Thanks for all the heart and sweat poured into this awesome mindmap and recommendations! It is a great resource!”
- Stefan Jäschke – “Terrific work Rafeeq Rehman – thanks for giving back to the community consistently over the years in so many ways.”
- Arvind Javali – “I listened to your podcast interview on CISO mindmap, very insightful, thanks for sharing”
- Ashoka Reddy – “Thank you, Rafeeq Rehman, for the knowledge, insight, time, and effort you have put into creating and sharing the #CISOMindMap. For #InformationSecurityManagers this is a gold standard that is priceless. It’s a little overwhelming to the point of being funny, but you’ve mapped my professional brain pretty nicely. For #BusinessLeaders this gives oversight to how we protect organizations, revealing our value and responsibilities.“
- Jas Puar – “Great timing. I’ve been looking at the 2022 version recently for some inspiration. Glad the 2023 version is available. The role is becoming bigger (cutting deeper across the entire business) and therefore more critical every year. More needs to be done to educate and raise awareness to change the direction of travel, otherwise an already thankless role, will very soon become an impossible one. Keep up the great work!”
- Steve Lodin – “Thanks again for your continued work here. I look at and keep a copy of every version you release!”
- Fernando Montenegro – “Really nice work, forwarded it to others. I really enjoy the “expiration date” aspect.”
- Georgeo X. Pulikkathara – “Rafeeq Rehman, good work on the CISO MindMap. My assessment is that this is a good framework for CISOs to approach all the areas we need to consider.”
- Rob Mukherjee – “This is brilliant, thanks Rafeeq. And couldn’t agree more with your comment in the first focus area. “Understand that merely having a backup is not enough. Ability to rebuild impacted systems and restore backups in a timely manner is crucial.” Spot on!! Think “restore”, not just backup!”
Acknowledgments
In addition to numerous infosec leaders who provide their input, we have a LinkedIn Group to gather suggestions and comments from the community. While many provided feedback, the following is a list of people and organizations who provided “specific suggestions” for improvements (in no particular order). If I missed anyone, please send me a message to make corrections.
- Jack Jones
- Gary Hayslip
- Michael Restivo
- Wes Sobbott
- Muath AlHomoud
- Ross Young
- Ross McNaughton
- Gerard Onorato
- Tony DeAngelo
- James J Azar
- Chris Hughes
- Izhar Mujaddidi
- Nadeem Iftikhar
- Ismail Cattaneo
- Andres Ricardo Almanza Junco
- Jack Jones
- Chad Sturgill
- Omar Khawaja
- Rodolphe Simonetti
- Scott Hawk
- Hisham Zahid
- Jerich Beason
- M Kashif Bukhari
- Chris Castaldo
- Atif Yusuf
- Jon Rogers
- Andi Baritchi
- Ricky Mehra
- Ahmed Kamel
- Tobias Ander
- Indy Dhami
- Matthew Thompson
- Marc Vael
- Christophe Foulon
Your input is highly appreciated!
References
[1] Wall Street Journal, Amazon Invests $2.7 Billions More in AI Startup, [link]
[2] Wall Street Journal, Open-Source Companies Are Sharing Their AI Free. Can They Crack OpenAI’s Dominance?, [link]
[3] NIST AI Risk Management Framework [link]
[4] Deloitte, Proactive Risk Management in Generative AI [link]
[5] Deloitte, The implications of Generative AI for businesses [link]
[6] CIO, The RACI matrix [link]
Copyright © 2012-2024 – Permission to use
This MindMap is copyrighted material. However it is absolutely free for all personal, business and professional purposes (like water and air). There are no strings attached, as long as it is not altered and not used to make money. When using this MindMap, please cite the source properly so that recipients can receive future updates.
Subscribe to Blog
To keep updated with new versions of CISO MindMap and other posts, subscribe to my blog here: