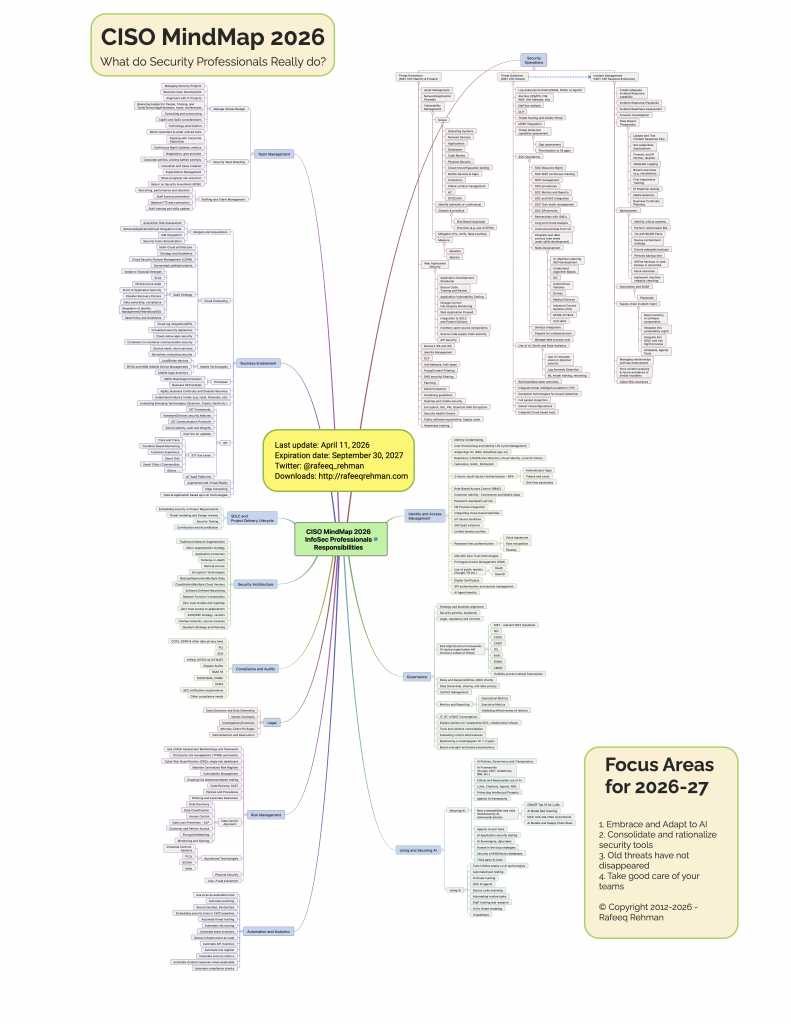
The job of a Chief Information Security Officer (CISO) is complex. Many individuals outside the realm of cybersecurity often underestimate the intricacies involved in a security professional’s role. Since its inception in 2012, the CISO MindMap has served as a valuable educational resource, offering insights into CISO responsibilities and aiding security professionals in crafting and enhancing their security programs. Continuously adapting to reflect the evolving landscape of cybersecurity, the CISO MindMap has been updated to accommodate the latest developments in the field. Here is the most recent iteration of the CISO MindMap for 2026, featuring numerous enhancements and recommendations for the next 12-18 months covering the year 2026-27.
And don’t forget to subscribe to my blog and follow me on LinkedIn.
Download High Resolution PDF File
The image in this blog post is PNG and may not be suitable for larger posters in your office. Please download a high resolution PDF version for larger printing by clicking here.
2026 Summary of Changes
With accelerating digitization of businesses, the responsibilities of security professionals are only increasing. Technology is changing fast, bringing new ways of doing business, continuous adoption of Cloud, and extremely fast evolving AI/GenAI technology. Not only the Infosec professionals are “expected” to deeply understand these technologies, they are also tasked with providing policies/guidance on how to secure them. For this reason, every year you find new items on the CISO MindMap. At the same time, some items are updated or removed from the CISO MindMap depending upon their relevance or obsolescence.
Here are things that have changed in the latest CISO MindMap.
- Removed Remote Work Category – Removed this category as remote work. This category was added during COVID-19 time as everyone was scrambling to manage risks related to work-from-home. As work-from-anywhere has become part of normal routine and risks are well-understood, there is no longer a need for separate sections.
- Significant Updates to “Using and Securing AI” – On top of updating the name of this category, significant changes have been made to reflect this fast paced area of technology.
- Consolidating old items – Some old elements in the MindMap have been consolidated and collapsed to make room for new items and, in few cases, to remove redundancies.
- Visual Improvements – Visual improvements are made to represent categories. The improvements will enable better reading.
Are you Accountable for Everything in the CISO MindMap?
Security is inherently a collaborative effort, and the role of the CISO entails providing consultative guidance in various areas outlined within the CISO MindMap. It’s crucial to discern between areas where direct ownership and accountability are necessary and those where consultation is the primary function. Within any organization, numerous stakeholders are involved, and a common pitfall is the lack of clearly defined boundaries for each role.
My recommendation is to establish a RACI (Responsible, Accountable, Consulted, Informed) matrix, which serves as a standardized methodology for delineating roles and responsibilities among stakeholders. By mapping out tasks and corresponding roles within this framework, clarity is achieved, ensuring that each stakeholder understands their level of involvement and contribution to the overall security landscape.
So yes, a CISO is probably not the only role to cover everything in this MindMap, hence, building alliances is important for success.
Important Things to Consider
Following are some important things to consider while using the CISO MindMap. Other than “you are not accountable for everything in the CISO MindMap” above, these considerations are to answer some questions that I have received in the past and may be on the minds of new readers.
- This MindMap is not “Perfect” – But it is good enough! From time to time I have received feedback about a missing industry term, or a process, or some technology that is not mentioned in the MindMap. Remember the focus is to cover major things, not be a comprehensive list of every security term or technology.
- Everything in the CISO MindMap does not apply to everybody – For example, compliance standards vary depending upon industry. Although many compliance standards are mentioned in the MindMap, a subset will apply to a particular organization.
- User of Controls Frameworks – A typical organization will follow a specific framework. Larger organizations may choose to create their own control framework if they have to comply with multiple standards/regulations.
Recommendations for 2026-2027
Each year, I offer my recommendations as a practitioner, drawing insights from information security leaders and industry trends. My approach strives for objectivity, steering clear of hype and focusing solely on what matters to a CISO. Though unintended biases may exist, the goal remains to propose actionable steps viable within a short to mid-range timeframe. These recommendations do not constitute future predictions; rather, they address the immediate needs for enhancing security programs.
Selecting a concise set of recommendations is always a challenge. Followers of the MindMap will notice both recurring suggestions from previous years and new additions, providing a blend of continuity and fresh insights.
I’m genuinely interested in hearing your perspective on these recommendations and understanding whether they resonate with your experiences and insights. Your feedback, whether in agreement or disagreement, provides valuable insights that can help refine and improve our approach to addressing security challenges. So, please feel free to share your thoughts and insights on these recommendations—whether you support them or have reservations—so we can engage in a constructive dialogue to further enhance our security strategies.
Recommendation 1: Embrace and Adapt to AI
Last year the recommendation about AI was “It is time for security GenAI”. A year before that I made a recommendation to “adopt a cautious approach towards GenAI”. A lot has happened in the last year and we have reached an inflection point where AI is out of the phase of “learn, test, and explore” to real business applications. Like other industries, impacts of AI are front and center in the security industry as well. Large Language Models (LLMs) are very mature and can do advanced reasoning. Not only are LLMs great at writing code, but are also finding decades old software bugs and vulnerabilities that have passed the scrutiny of the human eye and old tools.
This is a paradigm shift.
New AI tools are emerging, almost on a weekly, if not daily basis. There is a real possibility that many jobs in the security industry are going to evolve, and even be at risk, due to advancements in AI technologies.
What does this mean for CISO and security leaders? Following are some recommended actions.
- I assume that most organizations have already set up AI governance, responsible use of AI and have been training security staff on how to effectively use AI in daily operations.
- Update vulnerability management and AI application penetration testing processes to cater new needs for GenAI.
- Start building AI Agents that actually do useful work. I was not sure about this last year but agents are now being used very effectively.
- Explore vendor tools that are significantly more effective that older versions, such as SOC automation based upon AI agents, threat hunting, code analysis, etc.
- Enable the business to securely use AI. In some industries, organizations who don’t adopt AI at speed, they will risk extinction. Some organizations have already initiated “AI first” strategies for running their business.
AI is also introducing new risks that did not exist in the past. Some of these are listed below:
- AI tools are hungry for data. Know what is in your AI datalakes and knowledgebase used by different tools and whether good controls exist for protecting intellectual property and compliance with standards.
- Data leakage concerns related to third party tools and LLMs.
- Data Sovereignty – Geopolitical issues and data sovereignty is one of the immediate issues for many corporations. Can your business survive if upstream AI services and access to AI models is disrupted. Hosting may be shifting to an in-country or in-region data center to address concerns about access to AI in times of geopolitical risks.
I recommend referring to my blog post on “Eight Common Themes for AI Security Frameworks” which will help in building your framework for AI security.
Recommendation 2: Consolidate and Rationalize Security Tools
This is a continuation of a recommendation made last year and year before that. An average organization is using a large number of security tools, by some estimates as high as 47, according to a Ponemon survey. Yet many security leaders don’t know if Cybersecurity tools are working. Accumulating more security tools doesn’t necessarily lower risk; rather, it amplifies the necessity for maintaining expertise within security teams. Misconfigured security tools may become a liability in themselves. In some cases open source tools may work just fine as well and could be a good replacement for commercial tools.
The guiding principle is that no tool should be worth more than the value they bring and the risk they reduce. If interested, refer to my article “Managing Cybersecurity Tool Sprawl” for more explanation on this topic.
Recommendation 3: Old Threats have not Disappeared
While many are busy in AI related initiatives, we must not forget the basics and that old threats still exist.
- Ransomware is still happening.
- Web applications are still being exploited.
- Phishing is even more real, thanks to misuse of AI.
Many security professionals are painfully aware of the fact that, more often than not, security incidents and data breaches are a result of missing basic cyber hygiene. Please continue work on these basics such as:
- Enhance visibility into digital footprint with a target of obtaining full visibility.
- Shrink the attack surface for your organization as much as possible.
- Enhance API security. APIs are fueling growth of complex systems and are becoming an even bigger part of the overall infrastructure.
- Manage and reduce complexity. Remember complexity is the enemy of security.
- As an industry we are not very good at Third Party risk management. Keep finding better ways of doing so.
- Conduct a business impact analysis.
- Conduct exercises to thoroughly test backups that can be restored in a reasonable time. Note that backups could also be attacked/ ransomed.
- Purchase cyber insurance and make sure ransomware is included in the coverage.
- Focus on resilience and ability to restore operations in a timely manner.
Recommendation 4: Take Good Care of your Teams
We are living in a challenging and disruptive time, both from a technological change perspective and otherwise. Change is coming fast and furious. People are stressed and worried about the impact of AI on their jobs, pressure of learning and adapting to new technologies, worries about their families and their futures. Infosec professionals have already been under stress of constantly dealing with incidents. These new concerns are adding to their stress and well being.
It is incumbent on Cybersecurity leaders not only to manage their own stress but also guide their teams through this time of change. Learning and applying emotional intelligence in daily life is not a nice thing anymore, it is a necessity to understand and support your people.
How to Use CISO MindMap?
Have you ever been asked to explain what you do as a security professional? The CISO MindMap originates as an effort to answer this question and has evolved since then. It is a good tool for addressing this question and clarifying the intricacies of the role. Many professionals have attested to its efficacy in elucidating the complexities of the CISO position, particularly when communicating with a business audience.
Here are some ways in which the CISO MindMap proves to be immensely valuable:
- Facilitating conversations with fellow technology professionals.
- Instrumental in the design and refinement of security programs.
- Adopted by certain security vendors for raising awareness.
- Employed in CISO group discussions and community meetings.
- Aiding aspiring security professionals in understanding the industry landscape and charting their career paths.
- Serving as an educational and awareness-raising tool.
Obviously there is a lot on this MindMap. The stress on people who have these responsibilities is real. If nothing else, this MindMap should help leaders recognize that stress and do something about it. I covered this topic (stress) in my latest book Cybersecurity Arm Wrestling: Winning the perpetual fight against crime by building a modern Security Operations Center (SOC) as well.
What is Next: A training curriculum based upon CISO MindMap
In the past two years, I have been working on creating a training curriculum based upon CISO MindMap to cover three basic objectives:
- A comprehensive body of knowledge that covers theory and concept of information security.
- Hand on practice using open source tools that compliment the theory. This is important as it enables security professionals to practically use and implement the theoretical concepts.
- Business acumen required to be a successful security professional. I believe it is the most important part of the training for any security professional to be effective in their role.
I am exploring possibilities to launch this program through collaboration with other leaders and a certification program based upon this curriculum. The curriculum is in the final stages and will be published in the next 2-3 months.
Please follow Cybersecurity Learning Saturday on LinkedIn to keep updated about this program and join the LinkedIn Cybersecurity Learning Saturday group.
What are They Saying?
Following is a sample of comments on CISO MindMap 2025:
- Larry Whiteside Jr. wrote – This makes me smile, laugh, and weep a little each time you update it Rafeeq Rehman!! Thank you for keeping this up to date and relevant. I know its not easy, but your passion for it shows!!!
- Marc Vael wrote – Rafeeq Rehman thank you for being allowed to provide you with some suggestions. I use your CISO mindmap so often that I like giving you ideas to keep your one page visual security leadership overview in sync with evolutions in reality.
- Ken Kerrick wrote – Rafeeq Rehman, as always, we greatly appreciate the CISO MindMap and your dedication to creating this visualization. It’s a great resource for explaining what is on the “mind” of all CISOs.
- Mark Tomallo wrote – Thanks Rafeeq and everyone who provided input!! Such a helpful guide.
- Kristin Lowery wrote – It was a pleasure to collaborate on this. I believe it summarizes very critical and pragmatic measures useful for cybersecurity practitioners.
- Ross McNaughton wrote – Always a fantastic resource and the reference guide for the extent of the role!
- Jeremy Ault wrote – Great work! This reference is of great value that I have been referencing for several years now. Congratulations and thank you.
Following is a sample of comments on CISO MindMap post from 2024.
- Jack Jones wrote – “Really great piece of work, Rafeeq!”
- Jerich Beason CISO wrote – “This mind map has helped many CISOs explain the depth and breadth of their roles to so many executives…Thank you for allowing me to play a small role in this latest evolution.”
- Gary Hayslip CISO Softbank wrote – “thank you, my friend, for giving me the opportunity to participate in this year’s mindmap; I really like how the GenAI section came together. As always, thank you for continuing to develop this amazing resource and providing it to our #community”
- Omar Khawaja CISO wrote – “What a comprehensive list!”
- Atif Yusuf wrote – “Great job. Once again ! I especially like inclusion of “Business Resilience” and “Building a brand“
- Ross McNaughton CISO at Gulf Bank wrote – “As always, a great resource showcasing our field. Appreciated for all your efforts in maintaining and enhancing it constantly”
Following are some comments on CISO MindMap LinkedIn post from 2023.
- Michael Restivo – “One of the most valuable documents around. Love this Rafeeq.”
- Chris Novak – “Always a great asset! Thanks for all that you do for the cybersecurity community!”
- Muath AlHomoud – “Great insight Rafeeq Rehman always inspiring”
- Christophe Foulon – “Insightful as always, Rafeeq Rehman”
- Matthew P. – “Thanks for updating this. I think this makes a really useful tool when talking to the next generation about careers in security being able to demonstrate the breadth of what we can get involved in is quite eye opening”
- David Elfering – “Thank you! I review security programs as part of my work; your outline is fantastic. As a CISO, I regularly reviewed it, and as a consultant/advisor, I can see even more clearly how others would benefit.”
- Alan Ng – “Thanks for all the heart and sweat poured into this awesome mindmap and recommendations! It is a great resource!”
- Stefan Jäschke – “Terrific work Rafeeq Rehman – thanks for giving back to the community consistently over the years in so many ways.”
- Arvind Javali – “I listened to your podcast interview on CISO mindmap, very insightful, thanks for sharing”
- Ashoka Reddy – “Thank you, Rafeeq Rehman, for the knowledge, insight, time, and effort you have put into creating and sharing the #CISOMindMap. For #InformationSecurityManagers this is a gold standard that is priceless. It’s a little overwhelming to the point of being funny, but you’ve mapped my professional brain pretty nicely. For #BusinessLeaders this gives oversight to how we protect organizations, revealing our value and responsibilities.“
- Jas Puar – “Great timing. I’ve been looking at the 2022 version recently for some inspiration. Glad the 2023 version is available. The role is becoming bigger (cutting deeper across the entire business) and therefore more critical every year. More needs to be done to educate and raise awareness to change the direction of travel, otherwise an already thankless role, will very soon become an impossible one. Keep up the great work!”
- Steve Lodin – “Thanks again for your continued work here. I look at and keep a copy of every version you release!”
- Fernando Montenegro – “Really nice work, forwarded it to others. I really enjoy the “expiration date” aspect.”
- Georgeo X. Pulikkathara – “Rafeeq Rehman, good work on the CISO MindMap. My assessment is that this is a good framework for CISOs to approach all the areas we need to consider.”
- Rob Mukherjee – “This is brilliant, thanks Rafeeq. And couldn’t agree more with your comment in the first focus area. “Understand that merely having a backup is not enough. Ability to rebuild impacted systems and restore backups in a timely manner is crucial.” Spot on!! Think “restore”, not just backup!”
Acknowledgments
In addition to numerous infosec leaders who provide their input, we have a LinkedIn Group to gather suggestions and comments from the community. While many provided feedback, the following is a list of people and organizations who provided “specific suggestions” for improvements (in no particular order) in the previous years. I am extremely thankful to their support over the years.
If I missed anyone, or if anyone’s job title has changed, please send me a message to make corrections.
- Marc Vael, Esko Chief Digital Trust Officer
- Tammy Moskites, CEO & Founder, CISO
- Michael Restivo, Vice President | Cybersecurity Executive
- Wade Baker Ph.D. Cybersecurity Researcher, Entrepreneur, Professor
- Erik Wille, SVP & Chief Information Security Officer Cabinetworks Group
- Kristin Lowery – Vice President, Chief Security Officer at American Electric Power
- Omar Khawaja – CISO Databricks
- Ross McNaughton, Chief Information Security Officer at Gulf Bank
- Rahul Tyagi, Co-founder Safe Security
- Andi Baritchi, Vice President, Global Security Assurance, Compliance, Kyndryl
- Andres Ricardo Almanza Junco, Cybersecurity Strategist & vBISO | Founder of CISOS.CLUB
- Rodrigo Carvalho, Cybersecurity Service Manager, Brazil
- Peter Holcomb, CISO | Security Strategist & Advisor
- Muath AlHomoud, Director of Cybersecurity, D360 Bank
- Tony DeAngelo, VP, CISO at Encova Insurance
- James Azar, Global CISO | Founder X2
- Ahmed Kamal, Security ,Risk & Compliance at Nestlé
- Ty LeSane, Director of IT Security
- Walter Heffel, CISO at ENERSA
- Dominik Bredel, Director, Cyber Security bei PwC Deutschland
- Darren Kearsl, Security Professional @ Siemens Healthineers
- Dr. Toh Shang Yee, Head of Information Security at MCIS Insurance Berhad
Following is a list of those (in no particular order) who have contributed to CISO MindMap development in the past.
- Jack Jones
- Gary Hayslip
- Michael Restivo
- Wes Sobbott
- Muath AlHomoud
- Ross Young
- Ross McNaughton
- Gerard Onorato
- Tony DeAngelo
- James J Azar
- Chris Hughes
- Izhar Mujaddidi
- Nadeem Iftikhar
- Ismail Cattaneo
- Andres Ricardo Almanza Junco
- Jack Jones
- Chad Sturgill
- Omar Khawaja
- Rodolphe Simonetti
- Scott Hawk
- Hisham Zahid
- Jerich Beason
- M Kashif Bukhari
- Chris Castaldo
- Atif Yusuf
- Jon Rogers
- Andi Baritchi
- Ricky Mehra
- Ahmed Kamel
- Tobias Ander
- Indy Dhami
- Matthew Thompson
- Marc Vael
- Christophe Foulon
Your input is highly appreciated!